MCP Dev Summit NA 2026 Conference Recap
The MCP Dev Summit North America 2026 conference brought together leaders from Anthropic, AWS, Uber, Duolingo, Workato, Datadog, and dozens of other organizations to discuss the rapidly evolving landscape of the Model Context Protocol (MCP) ecosystem. A central theme was the transition from protocol adoption to enterprise production deployment — with a clear message that MCP is not only alive but becoming the standard integration layer for AI agents in enterprise environments.

MCP Growth and Adoption (David Soria Parra, Anthropic)
David Soria Parra, co-creator of MCP, opened with impressive adoption metrics:
- 100M+ SDK downloads per month across Python, TypeScript, Java, and other SDKs
- MCP reached in 16 months what took React approximately 3 years to achieve
- This growth signals a genuine ecosystem need for a standard to connect tools and systems to AI
The Enterprise Reality: Behind every corporate firewall, teams are quietly wiring MCP servers to systems of record — CRMs, wikis, Snowflake warehouses, and internal knowledge bases. These internal deployments represent some of the largest MCP usage, even though they're not visible on Twitter or Hacker News.
Protocol Evolution: Key improvements in the last 16 months include:
- Remote server support (moving beyond local-only)
- Authorization and security frameworks
- Structured outputs for code generation
- Long-running tasks primitive
- SDK stability tiers
- Extensions for experimentation
Roadmap Highlights:
- Transport evolution: Stateless approach for hyperscalers (coming in 1-2 months)
- Long-running tasks: For increasingly capable models
- Cross-app access: Seamless integration without manual auth flows
- Triggers: Webhooks for proactive agent engagement
- Streaming: Incremental results support
- Skills: Domain-specific knowledge bundled with MCP servers
The Context Window Problem
A recurring criticism of MCP is context window bloat — adding 50-100+ tools consumes tokens that should be used for actual work. David Soria Parra quantified the problem: 22% of a 200K context window was consumed by MCP tool definitions alone before optimization.
But speaker after speaker made the same point: this is a client implementation problem, not a protocol problem.
"Context window is not an MCP problem. It's a client problem. Solvable." — David Soria Parra
Solutions Emerging
| Approach | How It Works | Champion |
|---|---|---|
| Tool search | Discover tools on demand, not all at once | Anthropic (Claude Code), Cursor |
| CLI wrapping | Expose tools as CLI commands; load only when needed | AWS (vendor config) |
| Code mode | LLM writes code that calls MCP tools instead of function calling | Cloudflare, Anthropic |
| Vendor config | Server authors specify which tools to inject vs. defer | AWS |
| Progressive disclosure | Load tools contextually based on task | Uber (roadmap) |
MCPC: The Universal MCP CLI Client (Jan Čurn, Apify)
Jan Čurn, founder and CEO of Apify, introduced MCPC — a universal MCP command-line client that maps MCP commands to intuitive CLI commands. The insight: LLMs are trained on millions of lines of shell scripts and code, making them far more accurate at generating CLI commands than at function calling (a synthetic construct with less training data).
Cloudflare prototyped code mode and reported dramatically reduced token usage and increased accuracy, especially when chaining tool calls. Anthropic independently confirmed these results. MCPC makes this practical by providing a thin CLI wrapper around the MCP protocol — with shared credential storage across agents.
Enterprise Implementations
| Company | Context Window Approach |
|---|---|
| AWS | Vendor specifies in config which tools to inject directly vs. surface as CLI |
| Uber | Tool search in roadmap — discover tools automatically, load on demand |
| Duolingo | 180+ tools across 50+ servers; mix of direct injection and CLI access |
Enterprise Scale Deployments
Amazon Web Services (James Hood)
James Hood, a 16-year Amazon veteran and Principal Engineer, shared Amazon's journey:
- Tens of thousands of builders in Amazon's internal AI community
- MCP is "the most popular way to connect agents to internal systems"
- AWS employs a core maintainer (Claire LeBori) contributing to MCP
- Key contributions: elicitation primitive, structured outputs, tasks primitive
Internal Registry: Amazon built an internal registry for MCP servers and agent configurations, treating agent configurations as a first-class primitive. This enables:
- Centralized discovery and sharing
- Security categorization by "lethal trifecta" properties (private data + untrusted content + external communication)
- Configuration-level scanning for problematic agent combinations
Context Window Solution: Progressive disclosure — injecting some tools directly, wrapping others in CLI interfaces for on-demand discovery. This is not an MCP protocol problem, but a client implementation problem.
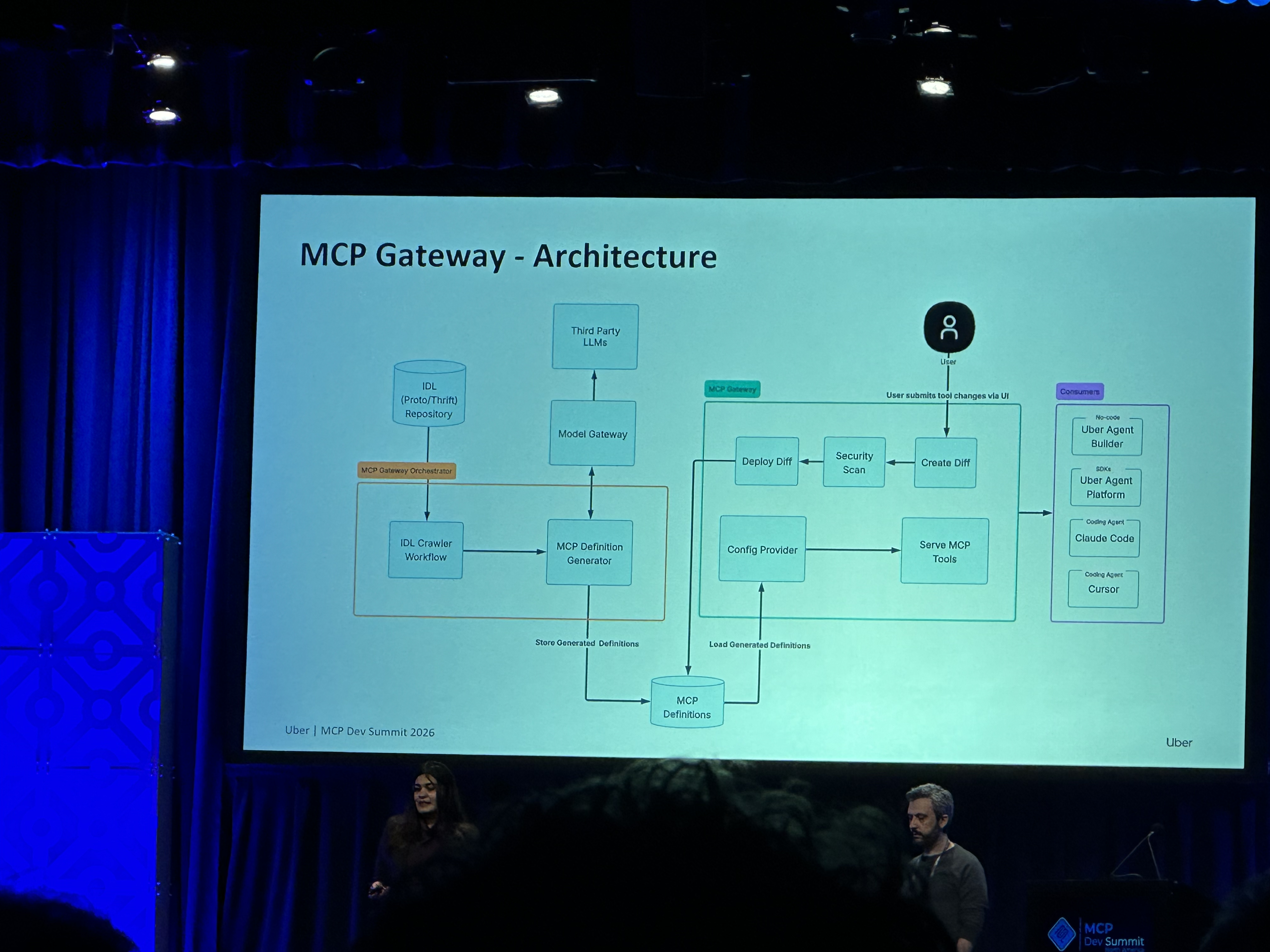
Uber (Meghana Somasundara & Rush Tehrani)
Uber's scale is staggering:
- 5,000+ engineers with 90%+ using AI weekly
- 10,000+ services across their architecture
- 1,500+ internal agents with 60,000+ executions per week
MCP Gateway & Registry: Uber built a control plane for all MCP interactions:
- Automatic translation of service endpoints to MCP tools
- Service owners stay in control of what gets exposed
- PII redaction and authorization integration
- Full observability and audit trails
Three Consumption Surfaces:
- Uber Agent Builder — No-code agent platform (thousands active monthly)
- Uber Agent SDK — Code-first solution for top use cases (grocery assistant, care coordination, customer support)
- Coding Agents — Claude Code, Cursor, and "Minions" (background agents) producing 1,800 code changes/week

Duolingo (Aaron Wang)
Duolingo's AI Slackbot demonstrates MCP's power for internal productivity:
- 180+ MCP tools connected to a single Slackbot
- 30+ MCP servers supported internally
- 250+ weekly users (30% of the company)
- 80% approval rate on responses
Key Implementation Details:
- Centralized "MCP store" for discovery
- Standardization strategy: fork open-source servers, add auth, host internally
- Internal Python library for converting services to MCP servers
- Security principles: no write operations without human approval, sandboxed environment, no side-channel between users
Open Source: Duolingo open-sourced the core application code at github.com/duolingo/slack-ai-agents
Architectural Patterns for Enterprise MCP
The Gateway and Registry Pattern (Sheng Liang, Obot)
Sheng Liang (CEO of Obot, formerly Rancher Labs) emphasized two essential pieces of technology for enterprises:
- MCP Gateway — Control point for what's happening across the organization
- MCP Registry — Single source of truth for discovery
Key Insight: The agent development framework itself is changing. What used to be ReAct loops, then workflows, is now becoming skills + generated code. The MCP layer is taking over what SDKs and frameworks used to handle.
Security Layers:
- MCP gateway for access control
- LLM gateway for model visibility
- Software supply chain filtering
- Isolated runtime (enterprise agents shouldn't run on desktops)
- Elevated access control layer
Vendor Landscape
A third to half of vendors at the conference were providing variations of gateway/registry solutions:
| Company | Gateway | Registry | Key Feature |
|---|---|---|---|
| Uber | Yes | Yes | LLM generates tool definitions from 10,000+ service IDLs |
| Obot | Yes | Yes | Skills + supply chain filtering |
| AWS | Yes | Yes | Agent configs + "lethal trifecta" security categorization |
| Duolingo | Yes | Yes | Centralized "MCP store" for discovery |
Skills: The New Abstraction
Skills are emerging as a key primitive — domain-specific knowledge bundles (recipes) for using MCP tools, shareable across teams.
"Think of skills as recipes for using MCPs — shareable across Uber teams." — Rush Tehrani
"Agents I see today look like skills — some markdown files, and code generated by a code generator." — Sheng Liang
Registries are evolving beyond just MCP servers: "You don't just see MCP registry anymore; you see skills too." — Sheng Liang
The Agent Control Plane (Workato)
Adam Seligman (CTO) and Zayne Turner introduced the Agent Control Plane concept — a framework for balancing autonomy and control:
Two Layers:
- Reasoning Layer (LLM, agents) — Probabilistic, makes decisions
- Control Plane — Deterministic, handles governance, auth, business logic
Seven Factors for Agent Control Plane:
| Factor | Description |
|---|---|
| Governance Operations | Protocols are thin; handle enterprise concerns yourself |
| Deterministic Mutations | Control plane owns all creates/writes/deletes |
| Intent-Based Communication | Tool calls about intent, not implementation details |
| Founded Access | Least privilege for probabilistic stakeholders |
| Safe Retries | Different retry patterns for stateless callers |
| Appropriate Errors | Error messages designed for reasoning callers |
| Structural Observability | Observability by design, not just logging |
Resource: White paper at workato.com/sevenfactors
Security Architecture: The Lethal Trifecta and Defense in Depth
A critical security concept emerged from James Hood's presentation: the "Lethal Trifecta" (Simon Willison's concept). Agents with all three of these properties create data exfiltration risk:
- Access to private data (read tools)
- Exposure to untrusted content (external inputs)
- Ability to communicate externally (write/network tools)
"The lethal trifecta can occur even if you only have trustworthy servers and trustworthy tools. Good tools can be composed into something that could allow for bad actions."
Amazon's internal registry categorizes every tool by these properties and scans agent configurations for problematic combinations.
Enterprise Security Layers:
| Layer | Purpose | Implementation |
|---|---|---|
| MCP Gateway | Access control | Tool filtering, authorization |
| LLM Gateway | Model visibility | See what's sent to the model (gateway alone can't) |
| Supply Chain | Dependency security | Scan MCP servers for compromise |
| Isolated Runtime | Containment | Containers, not desktops |
Defense in Depth: No single layer is sufficient, but combined they progressively reduce risk: tool confirmations → annotations → LLM-as-judge → static scanning → sandboxing → policy engines → real-time monitoring.
The MCP Security Workshop demonstrated that even official MCP servers can be silently compromised through fork attacks — passing all tests while exfiltrating data. A real-world incident with a popular email MCP server (Postmark) underscored the supply chain risk.
Building Production-Ready Agents (Datadog)
Diamond Bishop (Director of Engineering AI, Datadog) shared lessons from deploying 100+ agents:
Products in Production:
- Bits AI SRE — Automated incident investigation
- Bits AI Dev — Code generation for errors and latency issues
- Security Analyst — Automated security investigations
Key Lessons:
Code Agent-First: Every interface should be agent-friendly. Don't make everything require human UI interaction. Build APIs, CLIs, and agent-native interfaces.
Proactive Over Reactive: Background, long-running, event-driven agents are more valuable than chat-based interactions. Use durable execution (Temporal), containers, and sandboxes.
Eval and Monitoring: You can't improve what you don't measure. Build a living, breathing eval system. Make it available via MCP so agents can help improve themselves.
Stay Agnostic: Don't build for one model or framework. "Whoever is best today will probably not be best tomorrow." Build for portability with good memory systems.
Multiplayer: Design for human-human, human-agent, and agent-agent interactions with appropriate communication channels.
The Agentic AI Foundation
The conference also highlighted the Agentic AI Foundation (AIF), which now governs MCP:
- Governing Board — Strategic direction
- Technical Steering Committee — Technical decisions
- 7 Working Groups — 500+ participants already
- Identity & Trust Working Group — 150 members from 66 organizations
Project Lifecycle: AIF now has a documented process for accepting projects (Growth, Impact, and Emeritus stages), enabling new projects to join the foundation.

The Road Ahead
Key themes for the coming year:
Protocol Maturation:
- Stateless transport for hyperscale deployments
- Long-running tasks as a first-class primitive
- Cross-app authentication
- Triggers for proactive agents
- Streaming for incremental results
Enterprise Adoption:
- Gateway and registry patterns becoming standard
- Security categorization and governance frameworks
- Skills as recipes for MCP usage
- Agent configurations as shareable primitives
Developer Experience:
- SDK ergonomics improvements (Python, TypeScript)
- Better clients with progressive discovery
- Composability through code, not just tool calls
- Model-agnostic and framework-agnostic architectures
Operational Excellence:
- Eval systems integrated into development lifecycle
- Observability by design
- Durable execution for production agents
- Software supply chain security
Key Takeaways
- MCP is not dead — It's the foundation for enterprise agent strategies at Amazon, Uber, Duolingo, and beyond
- Gateway + Registry — Essential architecture for enterprise deployments
- Control plane matters — Deterministic layer for governance, auth, and business logic
- Context window is solvable — Progressive disclosure, tool search, CLI wrapping
- Skills are emerging — Recipes for MCP usage, shareable across teams
- Evals are non-negotiable — Continuous improvement through measurement
- Stay agnostic — Models and frameworks change; build for portability

Resources
- MCP Specification: modelcontextprotocol.io
- Agentic AI Foundation: aifoundation.org
- Workato Seven Factors: workato.com/sevenfactors
- Duolingo Slack AI Agents: github.com/duolingo/slack-ai-agents
- MCP Dev Summit: events.linuxfoundation.org/mcp-dev-summit-north-america/
Conference: April 1-3, 2026 | New York City